ArangoDB v3.10 reached End of Life (EOL) and is no longer supported.
This documentation is outdated. Please see the most recent stable version.
Security and access control in ArangoGraph
This guide explains which access control concepts are available in ArangoGraph and how to use them
The ArangoGraph Insights Platform has a structured set of resources that are subject to security and access control:
- Organizations
- Projects
- Deployments
For each of these resources, you can perform various operations. For example, you can create a project in an organization and create a deployment inside a project.
Locked resources
In ArangoGraph, you can lock the resources to prevent accidental deletion. When a resource is locked, it cannot be deleted and must be unlocked first.
The hierarchical structure of the resources (organization-project-deployment) is used in the locking functionality: if a child resource is locked (for example, a deployment), you cannot delete the parent project without unlocking that deployment first.
Policy
Various actions in ArangoGraph require different permissions, which can be granted to users via roles.
The association of a member with a role is called a role binding. All role bindings of a resource comprise a policy.
Roles can be bound on an organization, project, and deployment level (listed in the high to low level order, with lower levels inheriting permissions from their parents). This means that there is a unique policy per resource (an organization, a project, or a deployment).
For example, an organization has exactly one policy, which binds roles to members of the organization. These bindings are used to give the users permissions to perform operations in this organization. This is useful when, as an organization owner, you need to extend the permissions for an organization member.
How to view, edit, or remove role bindings of a policy
Decide whether you want to edit the policy for an organization, a project, or a deployment:
- Organization: In the main navigation, click the Organization icon and then click Policy.
- Project: In the main navigation, click the Dashboard icon, then click Projects, click the name of the desired project, and finally click Policy.
- Deployment: In the main navigation, click the Dashboard icon, then click Deployments, click the name of the desired deployment, and finally click Policy.
To delete a role binding, click the Recycle Bin icon in the Actions column.
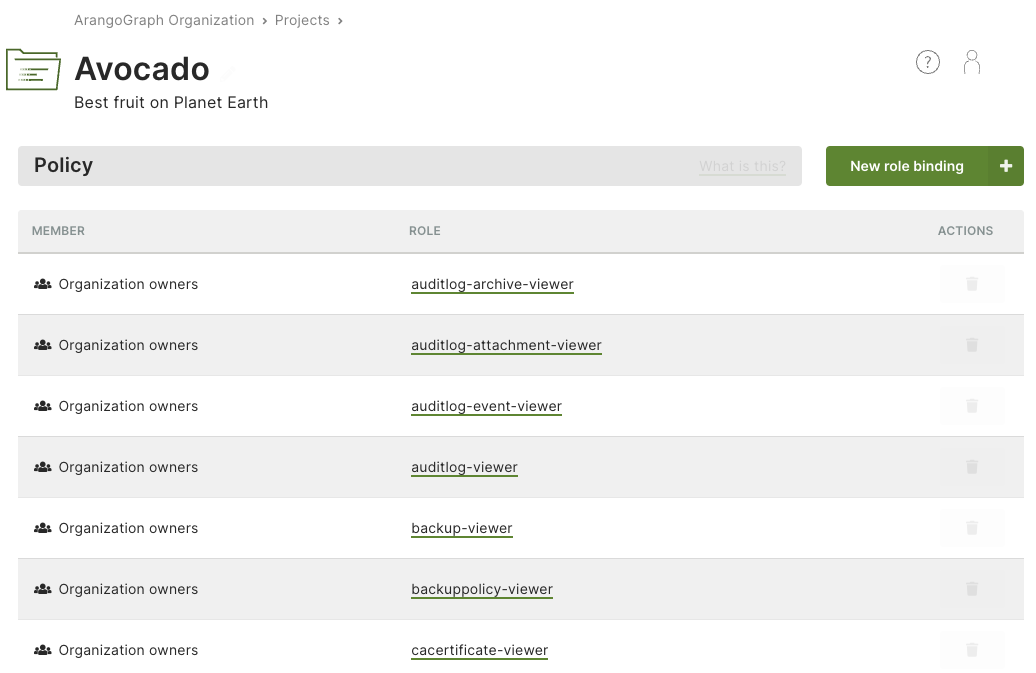
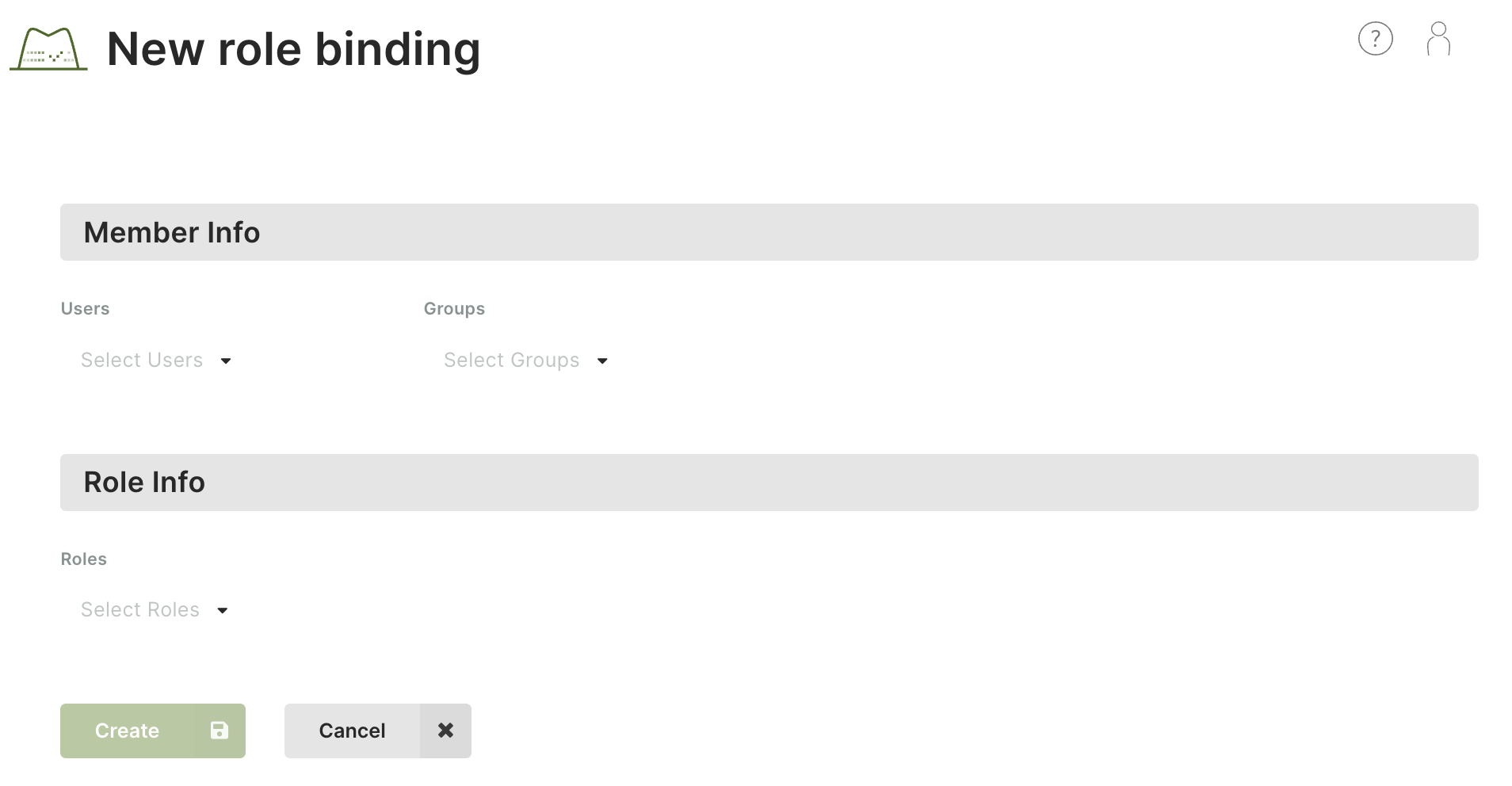
How to add a role binding to a policy
- Navigate to the Policy tab of an organization, a project or a deployment.
- Click the New role binding button.
- Select one or more users and/or groups.
- Select one or more roles you want to assign to the specified members.
- Click Create.
Roles
Operations on resources in ArangoGraph require zero (just an authentication) or more permissions. Since the number of permissions is large and very detailed, it is not practical to assign permissions directly to users. Instead, ArangoGraph uses roles.
A role is a set of permissions. Roles can be bound to groups (preferably) or individual users. You can create such bindings for the respective organization, project, or deployment policy.
There are predefined roles, but you can also create custom ones.

Predefined roles
Predefined roles are created by ArangoGraph and group related permissions together.
An example of a predefined role is deployment-viewer. This role
contains all permissions needed to view deployments in a project.
Predefined roles cannot be deleted. Note that permissions linked to predefined roles vary between organization owners and organization members.
List of predefined roles and their permissions
The roles below are described following this pattern:
Role description (role ID):
Permission
Audit Log Admin (auditlog-admin):
audit.auditlog.createaudit.auditlog.deleteaudit.auditlog.getaudit.auditlog.listaudit.auditlog.set-defaultaudit.auditlog.test-https-post-destinationaudit.auditlog.update
Audit Log Archive Admin (auditlog-archive-admin):
audit.auditlogarchive.deleteaudit.auditlogarchive.getaudit.auditlogarchive.list
Audit Log Archive Viewer (auditlog-archive-viewer):
audit.auditlogarchive.getaudit.auditlogarchive.list
Audit Log Attachment Admin (auditlog-attachment-admin):
audit.auditlogattachment.createaudit.auditlogattachment.deleteaudit.auditlogattachment.get
Audit Log Attachment Viewer (auditlog-attachment-viewer):
audit.auditlogattachment.get
Audit Log Event Admin (auditlog-event-admin):
audit.auditlogevent.deleteaudit.auditlogevents.get
Audit Log Event Viewer (auditlog-event-viewer):
audit.auditlogevents.get
Audit Log Viewer (auditlog-viewer):
audit.auditlog.getaudit.auditlog.list
Backup Administrator (backup-admin):
backup.backup.copybackup.backup.createbackup.backup.deletebackup.backup.downloadbackup.backup.getbackup.backup.listbackup.backup.restorebackup.backup.updatebackup.feature.getdata.deployment.restore-backup
Backup Viewer (backup-viewer):
backup.backup.getbackup.backup.listbackup.feature.get
Backup Policy Administrator (backuppolicy-admin):
backup.backuppolicy.createbackup.backuppolicy.deletebackup.backuppolicy.getbackup.backuppolicy.listbackup.backuppolicy.updatebackup.feature.get
Backup Policy Viewer (backuppolicy-viewer):
backup.backuppolicy.getbackup.backuppolicy.listbackup.feature.get
Billing Administrator (billing-admin):
billing.config.getbilling.config.setbilling.invoice.getbilling.invoice.get-preliminarybilling.invoice.get-statisticsbilling.invoice.listbilling.organization.getbilling.paymentmethod.createbilling.paymentmethod.deletebilling.paymentmethod.getbilling.paymentmethod.get-defaultbilling.paymentmethod.listbilling.paymentmethod.set-defaultbilling.paymentmethod.updatebilling.paymentprovider.list
Billing Viewer (billing-viewer):
billing.config.getbilling.invoice.getbilling.invoice.get-preliminarybilling.invoice.get-statisticsbilling.invoice.listbilling.organization.getbilling.paymentmethod.getbilling.paymentmethod.get-defaultbilling.paymentmethod.listbilling.paymentprovider.list
CA Certificate Administrator (cacertificate-admin):
crypto.cacertificate.createcrypto.cacertificate.deletecrypto.cacertificate.getcrypto.cacertificate.listcrypto.cacertificate.set-defaultcrypto.cacertificate.update
CA Certificate Viewer (cacertificate-viewer):
crypto.cacertificate.getcrypto.cacertificate.list
Dataloader Administrator (dataloader-admin):
dataloader.deployment.import
Deployment Administrator (deployment-admin):
data.cpusize.listdata.deployment.createdata.deployment.create-test-databasedata.deployment.deletedata.deployment.getdata.deployment.listdata.deployment.pausedata.deployment.rebalance-shardsdata.deployment.resumedata.deployment.rotate-serverdata.deployment.updatedata.deployment.update-scheduled-root-password-rotationdata.deploymentfeatures.getdata.deploymentmodel.listdata.deploymentprice.calculatedata.diskperformance.listdata.limits.getdata.nodesize.listdata.presets.listmonitoring.logs.getmonitoring.metrics.getnotification.deployment-notification.listnotification.deployment-notification.mark-as-readnotification.deployment-notification.mark-as-unread
Deployment Content Administrator (deployment-content-admin):
data.cpusize.listdata.deployment.create-test-databasedata.deployment.getdata.deployment.listdata.deploymentcredentials.getdata.deploymentfeatures.getdata.deploymentmodel.listdata.deploymentprice.calculatedata.diskperformance.listdata.limits.getdata.nodesize.listdata.presets.listmonitoring.logs.getmonitoring.metrics.getnotification.deployment-notification.listnotification.deployment-notification.mark-as-readnotification.deployment-notification.mark-as-unread
Deployment Full Access User (deployment-full-access-user):
data.deployment.full-access
Deployment Read Only User (deployment-read-only-user):
data.deployment.read-only-access
Deployment Viewer (deployment-viewer):
data.cpusize.listdata.deployment.getdata.deployment.listdata.deploymentfeatures.getdata.deploymentmodel.listdata.deploymentprice.calculatedata.diskperformance.listdata.limits.getdata.nodesize.listdata.presets.listmonitoring.metrics.getnotification.deployment-notification.listnotification.deployment-notification.mark-as-readnotification.deployment-notification.mark-as-unread
Deployment Profile Viewer (deploymentprofile-viewer):
deploymentprofile.deploymentprofile.list
Example Datasets Viewer (exampledataset-viewer):
example.exampledataset.getexample.exampledataset.list
Example Dataset Installation Administrator (exampledatasetinstallation-admin):
example.exampledatasetinstallation.createexample.exampledatasetinstallation.deleteexample.exampledatasetinstallation.getexample.exampledatasetinstallation.listexample.exampledatasetinstallation.update
Example Dataset Installation Viewer (exampledatasetinstallation-viewer):
example.exampledatasetinstallation.getexample.exampledatasetinstallation.list
Group Administrator (group-admin):
iam.group.createiam.group.deleteiam.group.getiam.group.listiam.group.update
Group Viewer (group-viewer):
iam.group.getiam.group.list
IAM provider Administrator (iamprovider-admin):
security.iamprovider.createsecurity.iamprovider.deletesecurity.iamprovider.getsecurity.iamprovider.listsecurity.iamprovider.set-defaultsecurity.iamprovider.update
IAM provider Viewer (iamprovider-viewer):
security.iamprovider.getsecurity.iamprovider.list
IP allowlist Administrator (ipwhitelist-admin):
security.ipallowlist.createsecurity.ipallowlist.deletesecurity.ipallowlist.getsecurity.ipallowlist.listsecurity.ipallowlist.update
IP allowlist Viewer (ipwhitelist-viewer):
security.ipallowlist.getsecurity.ipallowlist.list
Metrics Administrator (metrics-admin):
metrics.endpoint.getmetrics.token.createmetrics.token.deletemetrics.token.getmetrics.token.listmetrics.token.revokemetrics.token.update
Migration Administrator (migration-admin):
replication.deploymentmigration.createreplication.deploymentmigration.deletereplication.deploymentmigration.get
MLServices Admin (mlservices-admin):
ml.mlservices.get
Notebook Administrator (notebook-admin):
notebook.model.listnotebook.notebook.createnotebook.notebook.deletenotebook.notebook.getnotebook.notebook.listnotebook.notebook.pausenotebook.notebook.resumenotebook.notebook.update
Notebook Executor (notebook-executor):
notebook.notebook.execute
Notebook Viewer (notebook-viewer):
notebook.model.listnotebook.notebook.getnotebook.notebook.list
Organization Administrator (organization-admin):
billing.organization.getresourcemanager.organization-invite.createresourcemanager.organization-invite.deleteresourcemanager.organization-invite.getresourcemanager.organization-invite.listresourcemanager.organization-invite.updateresourcemanager.organization.deleteresourcemanager.organization.getresourcemanager.organization.update
Organization Viewer (organization-viewer):
billing.organization.getresourcemanager.organization-invite.getresourcemanager.organization-invite.listresourcemanager.organization.get
Policy Administrator (policy-admin):
iam.policy.getiam.policy.update
Policy Viewer (policy-viewer):
iam.policy.get
Prepaid Deployment Viewer (prepaid-deployment-viewer):
prepaid.prepaiddeployment.getprepaid.prepaiddeployment.list
Private Endpoint Service Administrator (privateendpointservice-admin):
network.privateendpointservice.createnetwork.privateendpointservice.getnetwork.privateendpointservice.get-by-deployment-idnetwork.privateendpointservice.get-featurenetwork.privateendpointservice.update
Private Endpoint Service Viewer (privateendpointservice-viewer):
network.privateendpointservice.getnetwork.privateendpointservice.get-by-deployment-idnetwork.privateendpointservice.get-feature
Project Administrator (project-admin):
resourcemanager.project.createresourcemanager.project.deleteresourcemanager.project.getresourcemanager.project.listresourcemanager.project.update
Project Viewer (project-viewer):
resourcemanager.project.getresourcemanager.project.list
Replication Administrator (replication-admin):
replication.deployment.clone-from-backupreplication.deploymentreplication.getreplication.deploymentreplication.updatereplication.migration-forwarder.upgrade-connection
Role Administrator (role-admin):
iam.role.createiam.role.deleteiam.role.getiam.role.listiam.role.update
Role Viewer (role-viewer):
iam.role.getiam.role.list
SCIM Administrator (scim-admin):
scim.user.addscim.user.deletescim.user.getscim.user.listscim.user.update
User Administrator (user-admin):
iam.user.get-personal-dataiam.user.update
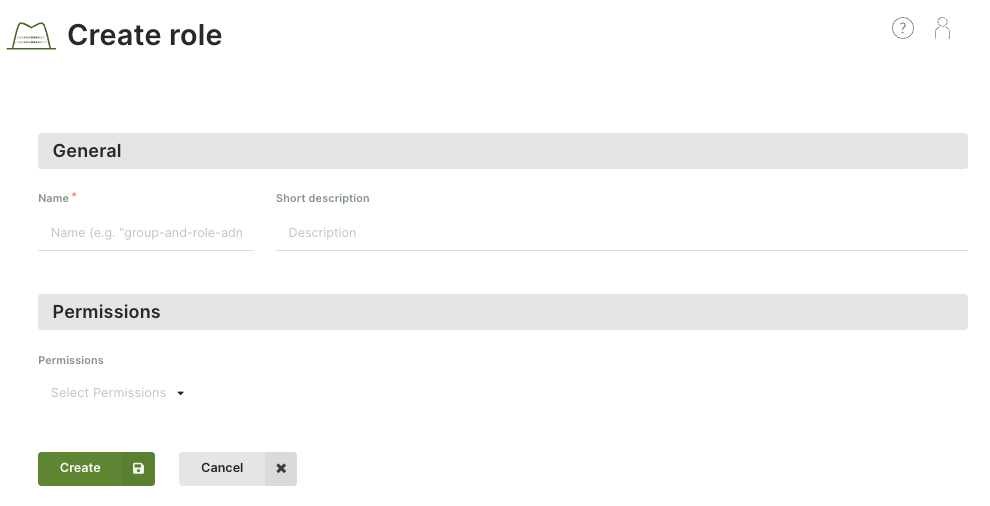
How to create a custom role
- In the main navigation menu, click Access Control.
- On the Roles tab, click New role.
- Enter a name and optionally a description for the new role.
- Select the required permissions.
- Click Create.
How to view, edit or remove a custom role
- In the main navigation menu, click Access Control.
- On the Roles tab, click:
- A role name or the eye icon in the Actions column to view the role.
- The pencil icon in the Actions column to edit the role. You can also view a role and click the Edit button in the detail view.
- The recycle bin icon to delete the role. You can also view a role and click the Delete button in the detail view.
Permissions
Each operation done on a resource requires zero (just authentication) or more permissions.
A permission is a constant string such as resourcemanager.project.create,
following this schema: <api>.<kind>.<verb>.
Permissions are solely defined by the ArangoGraph API.
| API | Kind | Verbs |
|---|---|---|
audit | auditlogarchive | delete, get, list |
audit | auditlogattachment | create, delete, get |
audit | auditlogevents | get |
audit | auditlogevent | delete |
audit | auditlog | create, delete, get, list, set-default, test-https-post-destination, update |
backup | backuppolicy | create, delete, get, list, update |
backup | backup | copy, create, delete, download, get, list, restore, update |
backup | feature | get |
billing | config | get, set |
billing | invoice | get, get-preliminary, get-statistics, list |
billing | organization | get |
billing | paymentmethod | create, delete, get, get-default, list, set-default, update |
billing | paymentprovider | list |
crypto | cacertificate | create, delete, get, list, set-default, update |
dataloader | deployment | import |
data | cpusize | list |
data | deploymentcredentials | get |
data | deploymentfeatures | get |
data | deploymentmodel | list |
data | deploymentprice | calculate |
data | deployment | create, create-test-database, delete, full-access, get, list, pause, read-only-access, rebalance-shards, restore-backup, resume, rotate-server, update, update-scheduled-root-password-rotation |
data | diskperformance | list |
data | limits | get |
data | nodesize | list |
data | presets | list |
deploymentprofile | deploymentprofile | list |
example | exampledatasetinstallation | create, delete, get, list, update |
example | exampledataset | get, list |
iam | group | create, delete, get, list, update |
iam | policy | get, update |
iam | role | create, delete, get, list, update |
iam | user | get-personal-data, update |
metrics | endpoint | get |
metrics | token | create, delete, get, list, revoke, update |
ml | mlservices | get |
monitoring | logs | get |
monitoring | metrics | get |
network | privateendpointservice | create, get, get-by-deployment-id, get-feature, update |
notebook | model | list |
notebook | notebook | create, delete, execute, get, list, pause, resume, update |
notification | deployment-notification | list, mark-as-read, mark-as-unread |
prepaid | prepaiddeployment | get, list |
replication | deploymentmigration | create, delete, get |
replication | deploymentreplication | get, update |
replication | deployment | clone-from-backup |
replication | migration-forwarder | upgrade-connection |
resourcemanager | organization-invite | create, delete, get, list, update |
resourcemanager | organization | delete, get, update |
resourcemanager | project | create, delete, get, list, update |
scim | user | add, delete, get, list, update |
security | iamprovider | create, delete, get, list, set-default, update |
security | ipallowlist | create, delete, get, list, update |
Permission inheritance
Each resource (organization, project, deployment) has its own policy, but this does not mean that you have to repeat role bindings in all these policies.
Once you assign a role to a user (or group of users) in a policy at one level, all the permissions of this role are inherited in lower levels - permissions are inherited downwards from an organization to its projects and from a project to its deployments.
For more general permissions, which you want to be propagated to other levels,
add a role for a user/group at the organization level.
For example, if you bind the deployment-viewer role to user John in the
organization policy, John will have the role permissions in all projects of
that organization and all deployments of the projects.
For more restrictive permissions, which you don’t necessarily want to be
propagated to other levels, add a role at the project or even deployment level.
For example, if you bind the deployment-viewer role to user John
in a project, John will have the role permissions in
this project as well as in all the deployments of it, but not
in other projects of the parent organization.
Inheritance example
- Let’s assume you have a group called “Deployers” which includes users who deal with deployments.
- Then you create a role “Deployment Viewer”, containing
data.deployment.getanddata.deployment.listpermissions. - You can now add a role binding of the “Deployers” group to the “Deployment Viewer” role.
- If you add the binding to an organization policy, members of this group will be granted the defined permissions for the organization, all its projects and all its deployments.
- If you add the role binding to a policy of project ABC, members of this group will be granted the defined permissions for project ABC only and its deployments, but not for other projects and their deployments.
- If you add the role binding to a policy of deployment X, members of this group will be granted the defined permissions for deployment X only, and not any other deployment of the parent project or any other project of the organization.
The “Deployment Viewer” role is effective for the following entities depending on which policy the binding is added to:
| Role binding added to → Role effective on ↓ | Organization policy | Project ABC’s policy | Deployment X’s policy of project ABC |
|---|---|---|---|
| Organization, its projects and deployments | ✓ | — | — |
| Project ABC and its deployments | ✓ | ✓ | — |
| Project DEF and its deployments | ✓ | — | — |
| Deployment X of project ABC | ✓ | ✓ | ✓ |
| Deployment Y of project ABC | ✓ | ✓ | — |
| Deployment Z of project DEF | ✓ | — | — |
Restricting access to organizations
To enhance security, you can implement the following restrictions via Oasisctl:
- Limit allowed authentication providers.
- Specify an allowed domain list.
Using the first option, you can limit which authentication providers are accepted for users trying to access an organization in ArangoGraph. The following commands are available to configure this option:
oasisctl get organization authentication providers- allows you to see which authentication providers are enabled for accessing a specific organizationoasisctl update organization authentication providers- allows you to update a list of authentication providers for an organization to which the authenticated user has access--enable-github- if set, allow access from user accounts authenticated via Github--enable-google- if set, allow access from user accounts authenticated via Google--enable-username-password- if set, allow access from user accounts authenticated via a username/password
Using the second option, you can configure a list of domains, and only users with email addresses from the specified domains will be able to access an organization. The following commands are available to configure this option:
oasisctl get organization email domain restrictions -o <your_organization_id>- allows you to see which domains are in the allowed list for a specific organizationoasisctl update organization email domain restrictions -o <your_organization_id> --allowed-domain=<domain_name1> --allowed-domain=<domain_name2>- allows you to update a list of the allowed domains for a specific organizationoasisctl update organization email domain restrictions -o <your_organization_id> --allowed-domain=- allows you to reset a list and accept any domains for accessing a specific organization
Using an audit log
To have a better overview of the events happening in your ArangoGraph organization, you can set up an audit log, which will track and log auditing information for you. The audit log is created on the organization level, then you can use the log for projects belonging to that organization.
To create an audit log
In the main navigation menu, click Access Control in the Organization section.
Open the Audit logs tab and click the New audit log button.
In the dialog, fill out the following settings:
Name - enter a name for your audit log.
Description - enter an optional description for your audit log.
Destinations - specify one or several destinations to which you want to upload the audit log. If you choose Upload to cloud, the log will be available on the Audit logs tab of your organization. To send the log entries to your custom destination, specify a destination URL with authentication parameters (the HTTP destination option).
The Upload to cloud option is not available for the free-to-try tier.Excluded topics - select topics that will not be included in the log. Please note, that some are excluded by default (for example,
audit-document).Enabling the audit log for all events will have a negative impact on performance.Confirmation - confirm that logging auditing events increases the price of your deployments.
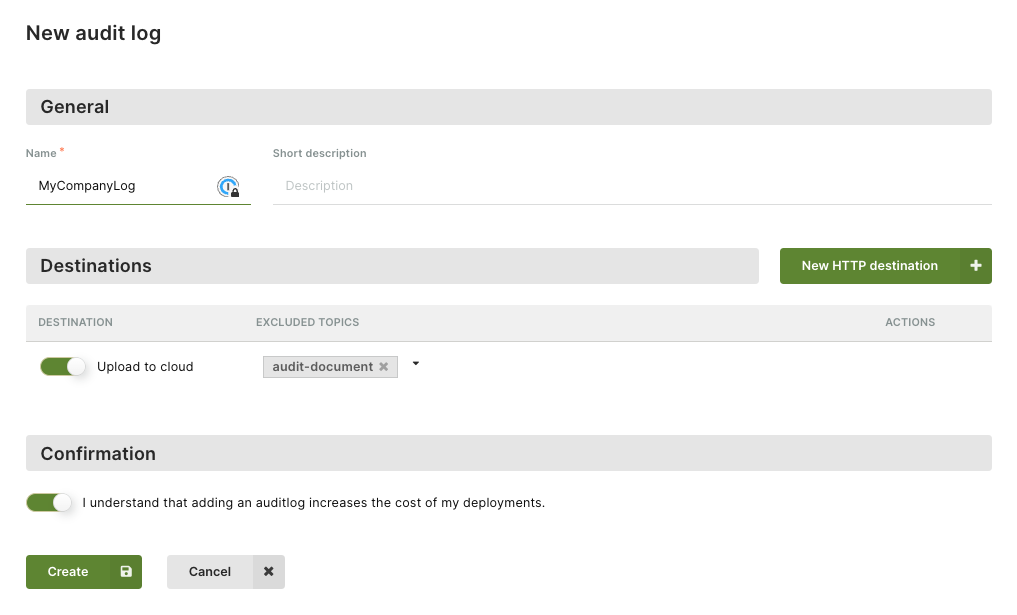
Click Create to add the audit log. You can now use it in the projects belonging to your organization.
